limiting user access to the system is considered what type of design activity?
By Robert Townsend on November 21, 2018
Groundwork –
Considered i of the nearly crucial assets in a company, access command systems agree significant value. The term 'access control' refers to "the command of access to organization resources after a user's account credentials and identity take been authenticated and admission to the system has been granted." Access control is used to identify a subject area (user/human) and to qualify the subject to access an object (data/resource) based on the required task. These controls are used to protect resources from unauthorized admission and are put into identify to ensure that subjects tin only access objects using secure and pre-approved methods. Three main types of access control systems are: Discretionary Admission Control (DAC), Office Based Access Control (RBAC), and Mandatory Access Command (MAC).
Discretionary Access Control (DAC) –
DAC is a type of access control organisation that assigns access rights based on rules specified by users. The principle behind DAC is that subjects tin can determine who has admission to their objects. The DAC model takes advantage of using access control lists (ACLs) and adequacy tables. Capability tables incorporate rows with 'bailiwick' and columns containing 'object'. The security kernel within the operating organization checks the tables to determine if access is immune. Sometimes a subject/program may just have access to read a file; the security kernel makes sure no unauthorized changes occur.
Implementation –
This popular model is utilized by some of the well-nigh popular operating systems, like Microsoft Windows file systems.
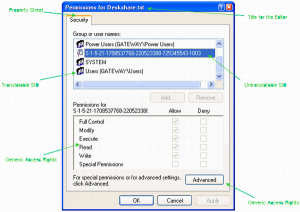
Effigy one – https://www.codeproject.com/Manufactures/10811/The-Windows-Access-Command-Model-Part-4
Role-Based Access Control (RBAC) –
RBAC, too known as a non-discretionary access control, is used when system administrators need to assign rights based on organizational roles instead of individual user accounts inside an organization. Information technology presents an opportunity for the organization to address the principle of 'least privilege'. This gives an private only the admission needed to do their job, since admission is connected to their chore.
Implementation-
Windows and Linux environments utilize something like past creating 'Groups'. Each group has individual file permissions and each user is assigned to groups based on their work function. RBAC assigns access based on roles. This is different from groups since users can belong to multiple groups just should only exist assigned to one role. Example roles are: accountants, programmer, among others. An accountant would simply proceeds access to resources that an accountant would need on the system. This requires the organization to constantly review the role definitions and have a procedure to alter roles to segregate duties. If not, part pitter-patter can occur. Role creep is when an individual is transferred to some other task/group and their access from their previous task stays with them.
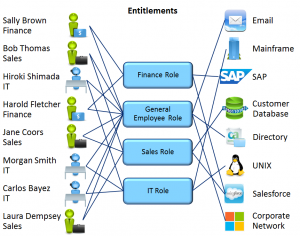
Figure 2 – https://www.docops.ca.com/ca-identity-governance/12-6-02-cr1/EN/getting-started/access-governance-and-rbac
Mandatory Access Control (MAC) –
Considered the strictest of all levels of access command systems. The design and implementation of MAC is commonly used by the government. Information technology uses a hierarchical approach to control access to files/resource. Nether a MAC environment, admission to resource objects is controlled by the settings divers by a arrangement ambassador. This means admission to resource objects is controlled past the operating arrangement based on what the system ambassador configured in the settings. It is not possible for users to modify admission command of a resource. MAC uses "security labels" to assign resource objects on a organisation. There are two pieces of information connected to these security labels: classification (high, medium, low) and category (specific department or project – provides "need to know"). Each user account is also assigned classification and category backdrop. This organisation provides users access to an object if both backdrop friction match. If a user has loftier classification simply is not part of the category of the object, then the user cannot access the object. MAC is the most secure access control merely requires a considerable amount of planning and requires a loftier system direction due to the constant updating of objects and account labels.
Implementation-
Other than the government's implementation of MAC, Windows Vista-8 used a variant of MAC with what they chosen, Mandatory Integrity Control (MIC). This type of MAC organization added integrity levels (IL) to process/files running in the login session. The IL represented the level of trust the object would have. Subjects were assigned an IL level, which was assigned to their access token. IL levels in MIC were: low, medium, high, and arrangement. Under this arrangement, access to an object was prohibited unless the user had the same level of trust, or college than the object. Windows limited the user to non beingness able to write or delete files with a higher IL. Information technology first compared IL levels, and then moved on to checking the ACLs to brand sure the correct permissions are in place. This system took advantage of the Windows DAC system ACLs and combined it with integrity levels to create a MAC environment.

Figure three – https://www.thewindowsclub.com/mandatory-integrity-control
Conclusion –
Admission controls are used to forestall unauthorized access to system resources. By implementing access control systems that fit your system, you can improve manage your assets. DAC, RBAC, and MAC admission control systems are models that have been used to create access control systems that provide reliability and security. Businesses with smaller applications volition find DAC to be easier to implement. Others with highly confidential or sensitive data may decide to use RBAC or MAC systems.
Sources –
https://www.tedsystems.com/iii-types-admission-control-which-right-building/
https://www.stor-guard.com/article/types-of-access-control-systems-for-effective-personnel-security-43
https://searchsecurity.techtarget.com/feature/CISSP-online-grooming-Inside-the-access-command-domain
https://searchsecurity.techtarget.com/definition/mandatory-admission-control-MAC
https://resources.infosecinstitute.com/cissp-admission-control-domain/#gref
https://www.techotopia.com/index.php/Mandatory,_Discretionary,_Role_and_Rule_Based_Access_Control
https://searchdatacenter.techtarget.com/answer/DAC-and-MAC-safety
http://world wide web.cs.cornell.edu/courses/cs5430/2015sp/notes/dac.php
Source: https://westoahu.hawaii.edu/cyber/best-practices/best-practices-weekly-summaries/access-control/
0 Response to "limiting user access to the system is considered what type of design activity?"
Post a Comment